This method utilizes PowerShell to discover the number of days since a local account password has been changed. For this process, we are going to take a look at the local Administrator account.
First, open PowerShell.
$admin = [ADSI]"WinNT://./Administrator,user"
This collected the Administrator object and placed it in a variable called $admin
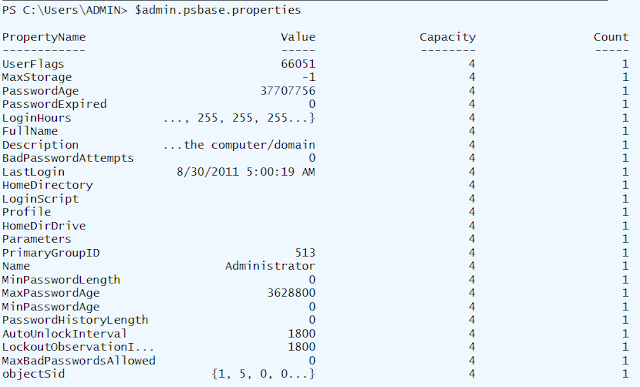
$Admin.PSBase.Properties
This will list some of the properties of this account.
The PasswordAge property reports the password age in seconds. To convert this to days, we will need to divid it by 86400 (60 seconds in a minute X 60 minutes in an hour X 24 hours in a day).
($Admin.PasswordAge.Value)/86400
436.432361111111
First the command evaluates the content in the parenthesis. This will be the value of the PasswordAge property as an integer value. Then we divide by 86400 seconds to get the result in days.
First, open PowerShell.
$admin = [ADSI]"WinNT://./Administrator,user"
This collected the Administrator object and placed it in a variable called $admin
$Admin.PSBase.Properties
This will list some of the properties of this account.
The PasswordAge property reports the password age in seconds. To convert this to days, we will need to divid it by 86400 (60 seconds in a minute X 60 minutes in an hour X 24 hours in a day).
($Admin.PasswordAge.Value)/86400
436.432361111111
First the command evaluates the content in the parenthesis. This will be the value of the PasswordAge property as an integer value. Then we divide by 86400 seconds to get the result in days.
Comments