Microsoft gave us a nice tool to use with the release of Windows Server 2008 R2 when working with server core. To set the IP address on Server Core 2008 R1, you would have to follow this procedure:
· Type netsh interface ipv4 show interfaces
· Press Enter
· Record the name of the interface you want to set a static IP address for. Sample output is below.
Idx Met MTU State Name
--- --- ----- ----------- -------------------
3 5 1500 Connected Local Area Connection
· Type netsh interface ipv4 set address name=3 source=static address=10.10.1.10 mask=255.255.0.0
· Optionally, you can add a gateway address by appending gateway=address to the end of the command.
· In the Name parameter, we used the Idx value. We could have also typed “Local Area Network”.
The above method still works if you need to batch file something. Now with the R2 version, you can use a menu based system thanks to SConfig.
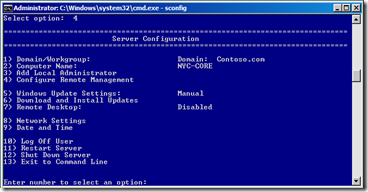
On you Server Core 2008 R2, log in and type sconfig.
Press 8 for Network Settings.
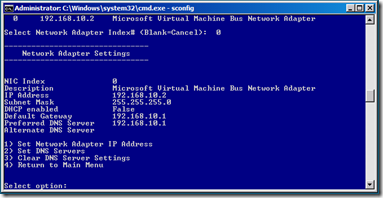
Select the index number for the network adapter that you want to configure. In this case, it will be 0.
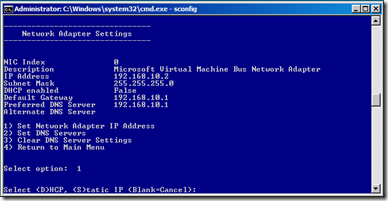
Press 1 to Set Network Adapter IP Address
We can set this server core for DHCP by pressing D. It will only take a few seconds for the change to take effect. Had this adapter already been set to DHCP, we could click S for Static address.
You will need to enter data for the IP Address, Subnet Mask, and Default Gateway.
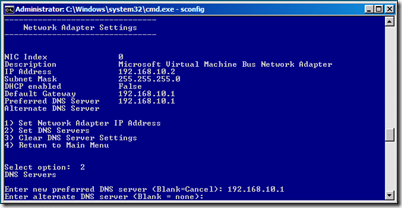
Once completed, you can set the DNS server if necessary by selecting 2
You will be given a chance to configure both a primary, and a secondary DNS server if you need to.
Once you are finished, press 4 to exit to the main menu and then 13, to exit SConfig.


Comments