The short answer is no. We do have the ability to import our PowerShell history from one session to another if we save that history to an XML file. We can then import that history into another session. The F7 and up arrow functionality in the PowerShell window is a feature of the window, not PowerShell. Here is an example.
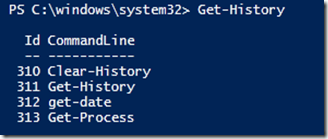
1. Open PowerShell and execute a couple of simple cmdlets.
2. Type Get-History and press Enter.
You can save this information to an xml file for import into another session
Get-History | Export-Clixml History.xml
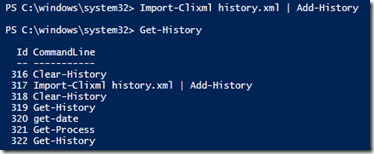
Either open another PowerShell session or type Clear-History to clear your current session’s history.
Now import your history back in by:
If you press F7, you will not get these items in the history window. You can still use them. Let’s execute the item in ID 312.

Comments