This question came from one of my Active Directory classes. To find the solution, I installed RSAT on a Windows 8 client. I also created a user named JYoder who is not a member of any special group. I also had to do a little bit of detective work to figure out a small piece of this puzzle.
The first real big problem is that I noticed the Last Name field is missing from the Delegate Control Wizard. We are missing the SN attribute which is the last name. Here is where the fun starts. On the client that you are using to delegate rights, Open dssec.dat You will find it in %Systemroot%\System32. Make a copy of this first and then open it in Notepad.
Now, scroll close to the bottom. You will notice that the file is divided into object types. Close to the bottom, you will find the User object. Look for the SN field in the user object. Make sure, you are in the user object.
Now, look for SN=7. Change this to SN=0. Save the changes
Now, close and re-open Active Directory Users and Computer.
Right click the OU that you want to delegate permissions to and select Delegate Control…
Click Next
Click Add
Select the user whom you want to delegate permissions to and click Check Names, and then OK
Click Next.
Click Create a custom task to delegate and click Next.
Select Only the following objects in the folder and then place a check by User objects.
Click Next
Uncheck General and check Property-specific
In the permissions list, place a check by:
- Write: AccountNameHistory
- Write: Display Name
- Write: First Name
- Write: Initials
- Write: Last Name
- Write: Logon Name
- Write: Logon Name (Pre Windows 2000)
- Write: Middle Name
- Write: msDS-LastKnownRDN
- Write: name
- Write: Name
Click Next
Click Finish
Log on to the client as the user you have delegated rights to.
Open Active Directory Users and Computers.
Inside the OU where you delegated this user the rights to rename an account, right click a user account and select Rename.
Type the display name for the new user and press Enter. This will open a Rename User box.
Change the necessary fields and click OK
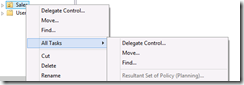
To show that I cannot use the RSAT tools to perform actions that I am not allowed to do, I simple right click the Sales OU. I can see that under all tasks, I am limited:
Also try some other functions to see that the Delegate Control Wizard did not give out more than you ask for.


Comments
Thanks
Go in the DSSEC file. I do not have one in front of me, but I believe you will find what you are looking for.
I'm glad this helped you out.
Jason