This one through me for a loop in class. While talking about what SYSPREP does to a client, one of the members of the class pointed me to a very interesting article. I have always been taught that the SID of the computer account is what Windows looks at for assigning security access. Well, take a minute to read this blog post from Mark Russinovich at Microsoft.
OK, let’s put this to the test. I took a VM from class and created an image of it. I then deployed this non syspreped image to another VM and started it up in the same environment as the original. The original was logged off and I had no trouble logging in. After taking snapshots of the new VM and the DC, I went ahead and renamed the VM to LON-CL3. In AD Users and Computers, the account associated with the original was renamed.
OK, I reapplied the snap shots and brought both identical VMs online. I was able to log in on both. On the original, I’m renamed the client and allowed it to reboot.
In the image below, you can see a client named LON-CL5. This is my renamed original. I was also able to successfully log in using the cloned that is still named LON-CL1. At this point, security is obviously looking at the SID.
Group Policy Updates
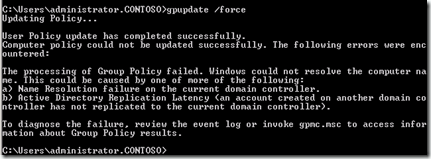
I was able to update group policy on the client that was renamed, but the clone with the original name could not update its policy.
This points to something other than the SID being used.
Resetting the computer account still allowed both clones to log in.
I’m out on this one as to what the computer account SID is used for. Keep an eye on Mark’s blog. It has so far generate 18 pages of comments.

Comments