The Snippet functionality in PowerShell is a really cool feature. It allows you to easily add templates to the ISE to help speed up your coding. Recently I added a new snippet and discovered that I messed up the description. Well, looking at the commands provided to us from the ISE Module, we do not have much of a choice when it comes to modifying the description, or even removing the snippet from the ISE.
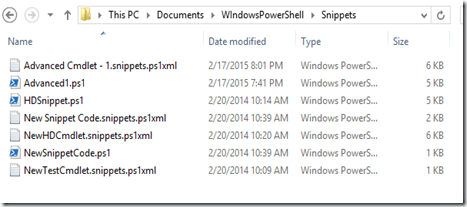
Well, here is how you fix that. Simply browse to your Documents\WindowsPowerShell\Snippets folder. Here you can see the file for my Advanced1 Snippet. It is called Advanced Cmdlet – 1.snippets.ps1xml.
Simply delete this file and restart the ISE. That is all that it takes.
In my situation, I just simply re-register the snippet with the correct description. Here is the code that I used to register the Snippet.
And here is what my description looks like:

PS C:\> Get-Command -Module ISE
CommandType Name Version Source
----------- ---- ------- ------
Function Get-IseSnippet 1.0.0.0 ISE
Function Import-IseSnippet 1.0.0.0 ISE
Function New-IseSnippet 1.0.0.0 ISE
Simply delete this file and restart the ISE. That is all that it takes.
In my situation, I just simply re-register the snippet with the correct description. Here is the code that I used to register the Snippet.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
$Text = (Get-Content -Raw -Path "C:\Users\JASON\Documents\WIndowsPowerShell\Snippets\Advanced1.ps1")
$Desc1 = "Advanced Cmdlet Template"
$Desc2 = "`n--------------------------------------------------"
$Desc3 = "`n Use when you need to be able to access remote"
$Desc4 = "`n clients with PowerShell Remoting."
$Desc5 = "`n---------------------------------------------------"
$Props = @{
"Title" = "Advanced Cmdlet - 1";
"Description" = $Desc1+$Desc2+$Desc3+$Desc4+$Desc5
"Author" = "Jason A. Yoder"
"Text" = $Text
"CaretOffset" = 10
}
New-IseSnippet @Props
|

Comments