Last week I delivered a Windows Server 2012 R2 class in Fort Wayne. I had a real neat idea from the class pop up during the Distributed File System (DFS) content. The class member’s situation was that he had over a terabyte of user home folders and redirected folders on a Windows Server 2003 R2 box and needed to move it to a Windows Server 2012 R2 box with minimal, if not zero, disruption to his 24-7 organization. DFS sounds like a good idea, but would the two versions of DFS work together?
This is part 1 of a 3 part series on how we accomplished this task.
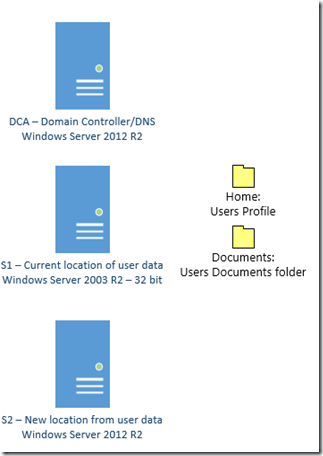
We started off with this configuration:
Our general process looks like this:
· Install DFS Namespace and replication on both servers (S1 and S2).
· Create a DFS Namespace on S1 that has references to both shares.
· Create a DFS Replication Group between S1 and S2.
· Change the GPOs to point to the new server.
· Disable S1 and verify that the clients are using S2.
· Bring S1 back online and remove the Replication.
· Remove DFS from S2.
In all honesty, the hardest part of this was trying to remember how to install Windows Server 2003. We struggled a bit to get it right. I may be an MCSE on Win 2003, but it has been a very long time. After we got the cob webs between my ears cleared up, we went to work.
Install DFS on S1 (Windows Server 2003 R2)
Insert the Windows Server 2003 R2 DVD (Or ISO file) in the DVD drive.
Click Start à All Programs à Administrative Tools à Manage Your Server.
Click Add or remove a role.
In the Configure Your Server Wizard, click Next.
On the Server Role page, click File Server à Next à Next.
In the Add File Server Role Wizard, click Next, and then click Replicate data to and from this server.
Follow any on screen instructions and then reboot the server.
Install DFS on S2 (Windows Server 2012 R2)
Open Windows PowerShell as an Administrator
Type (This is one continuous line):
Install-WindowsFeature -Name FS-DFS-Namespace,
FS-DFS-Replication -IncludeAllSubFeature -IncludeManagementTools -Restart
Tomorrow, we will add in the DFS Namespace and replication.
Comments