Originally this question was “How to force all new wireless networks to be Public.” I had very little luck with this one. I started looking into a PowerShell option for this, but that code was turning into a complex process. It then hit me, just make the two profiles the same in the firewall.
To do this, we are going to use the firewall on a Windows 7 client.
Open the Windows Firewall with Advanced Security.
Right click Windows Firewall with Advanced Security and then click Export Policy.
Save the policy to a network location.
Open Group Policy Management on a Windows 2008 R2 server or a Windows 7 Client with RSAT installed.
Create a new GPO, or used one that is scoped to reach all of your clients. I named my GPO Firewall.
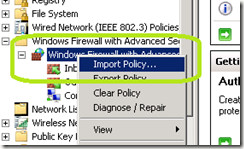
Edit the GPO and expand Computer Configuration / Policies / Windows Settings / Security Settings / Windows Firewall with Advanced Security / Windows Firewall with Advanced Security.
Right click Windows Firewall with Advanced Security and select Import Policy.
Click Yes at the warning.
Import the policy that you exported with the previous steps.
Now, go through the inbound and outbound rules. Anywhere you see the profile as only listing Private, mark it as also being set for Public. To do this, double click on a setting that is only set for Private.
Click the Advanced tab.
Check Public and then click OK.
Do this for all the inbound and outbound rules.
Now apply the GPO to the clients and the Public firewall profile will be just as restrictive as the Private profile. Should your user accidently click Private, no problem. They will have the same settings as the Public profile.
You will need to use this GPO to make any future firewall updates and remember to apply any changes to the Public profile to also include the Private profile.



Comments