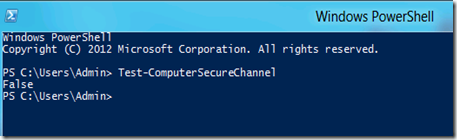
On a domain joined Windows Client, you may get an image like this:
(From Windows 8)
This means that the client computer’s account with the domain had a password change but for some reason your client does not know the password. This can happen if you restore your client operating system from a backup. To fix this, we would normally rejoin the client to the domain. This would cost us a reboot. Here is an alternative.
· Log into the client as a local administrator.
· Open PowerShell
· Type Test-ComputerSecureChannel
Notice the response back is False That means the secure channel cannot be negotiated between the client and the domain controller. The secure channel allows for your client to verify that it is talking with the correct domain controller. If the secure channel does not work, then you cannot log in. Here is how to fix this.
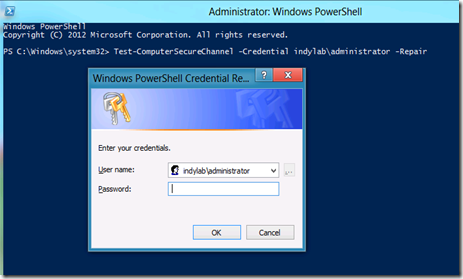
· Type Test-COmputerSecureChannel –Credential <Domain/DomainUser> -Repair and press Enter.
· Provide the domain users password and press Enter.
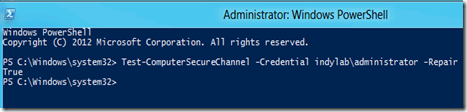
Notice the response is now True.
· Log off as a local user and log in as a domain user.
You should now be able to log in without a reboot.
This will also work on Windows 7.

Comments
Any suggestions to be able to run the command with a domain account?