Password Setting Object (PSO) is another name for Fine Grain Password Policies. These PSOs allowed us to set up a different password policy based on security group membership. For example, an employee who is working on a multi billion dollar drug might need to have more characters in their password and more frequent password changes than someone who does not handle critical company data. PSOs allow us to do that.
Up until now, PSOs were created with the ADSI Edit application or PowerShell. Now, we can use the Active Directory Administrative Center.
- Open the Active Directory Administrative Center.
- Change to Tree View.
- Expand System
- Click Password Settings Container
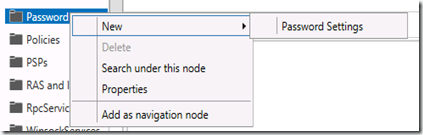
- Right Click Password Settings Container and then select New –> Password Settings.
Here you can see all the settings that go into a PSO. A few items to point out.
| Precedence | In the case of a conflict in which a user is a member of more than one group with different PSOs assigned to each group, the one with the Precedence number that is lower will be the effective PSO |
| Direct Applies To | If you do not any users or groups to the PSO it will not apply to anybody. |
Another nice feature of the AD Administrative Center is that you can easily see the precedence values that have been used and which PSO is using them.



Comments
I know this post was a yr ago but just to check if some pre-requisite is necessary to ensure i can create PSOs from AD Administrative Center.
Must the domain functional level be raise to 2012 for this to work?
The following link only mention 3 method for this to work but it is for 2008 - http://technet.microsoft.com/en-us/library/cc754461(v=ws.10).aspx
Hope you can clarify. Thanks