In Windows Server 2008 R2, We had a new, and very welcome feature added into our administrative tool bag. The Active Director Recycle Bin allowed us to bring back deleted objects from Active Directory without loosing any property of that object. Turning it on was an issue. Below is how you turn on the AD Recycle Bin in a 2008 R2 forest with a domain named. MCTNet.com.
1. Click Start, click Administrative Tools, right-click Active Directory Module for Windows PowerShell, and then click Run as administrator.
2. At the Active Directory module for Windows PowerShell command prompt, type the following command, and then press ENTER:
For this example, my domain is MCTNet.com.
Enable-ADOptionalFeature –Identity ‘CN=Recycle Bin Feature,CN=Optional Features,CN=Directory Service,CN=Windows NT,CN=Services,CN=Configuration,DC=MCTNet,DC=COM’ –Scope ForestOrConfigurationSet –Target ‘MCTNet.com’
With Server 2012, you now can now turn on the AD Recycle Bin in the GUI.
- On a 2012 Domain Controller, open Server Manager.
- Click Tools
- Click Active Directory Administrative Center.
- Right click the name of your domain (Contoso in this case) and select Enable Recycle Bin…
Notice that this is a one way operation just like in Server 2008 R2.
- Click Yes.
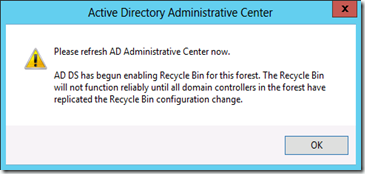
Your AD Recycle bin will be fully active once all the Domain Controllers have been notified.


Comments