Even though our domains are multimaster domains, not all functionality can be handled by each machine independently. For example, let’s take a look at the RID Master role.
And RID is what uniquely identifies all security objects in a domain. A security object is either a user, computer, group, or INetOrgPerson. Each of these objects have a Security Identifier (SID). A SID looks like this:
S-1-5-21-576790344-2948317706-4057815606-1702
To break this down:
| S | The string is a SID |
| 1 | The revision level |
| 5 | The identifier value. Possible identifier authority values are: 0 – Null Authority 1 – World Authority 2 – Local Authority 3 – Creator Authority 4 – Non-unique Authority 5 – NT Authority 9 – Resource Manager Authroity |
| 576790344-2948317706-4057815606 | Domain or local computer identifier |
| Relative Identifier (RID). This is unque in the domain. | 1702 |
Active Directory uses the SID to identify an object that can have security access assigned to it. You and I use the user name. the username name maps to a SID with the RID portion being unique in the domain. If two domain controller are handing our RIDs to new objects, there is a chance that two objects could get the same SID. This would allow the two different users to have the same access as the other one. With the RID Master being a single domain controller, this cannot happen.
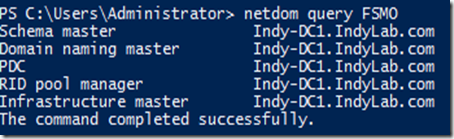
The easiest way to discover the FSMO (Flexible Single Master Operation) roles was to use NETDOM Query FSMO.
If you need to discover these roles in a PowerShell script, this would be difficult as the information is returned as a string of text. To execute the below PowerShell commands, you must do this on a client or server with the ActiveDirectory module installed.
Import-Module ActiveDirectory
$FSMOObj = New-Object PSObject
# Retrieve the Schema Master
$FSMOObj | Add-Member -MemberType NoteProperty -Name "Schema" -Value (Get-ADForest).SchemaMaster
# Retrieve the Domain Naming
$FSMOObj | Add-Member -MemberType NoteProperty -Name "DomainNaming" -Value(Get-ADForest).DomainNamingMaster
# Retrieve the PDC
$FSMOObj | Add-Member -MemberType NoteProperty -Name "PDC" -Value(Get-ADDomain).PDCEmulator
# Retrieve the Infrastructure Master
$FSMOObj | Add-Member -MemberType NoteProperty -Name "Infrasturcture" -Value(Get-ADDomain).InfrastructureMaster
# Retrieve the RID pool manager
$FSMOObj | Add-Member -MemberType NoteProperty -Name "RID" -Value(Get-ADDomain).RIDMaster
#Send the object to the Pipeline.
Write-Output $FSMOObj
This will send objects into the PowerShell pipeline that you can use in your code.
Comments