You will need to be logged in as an administrator (or elevate your privilege level) to complete this task.
First you need to register your Schema snap in before we can use it.
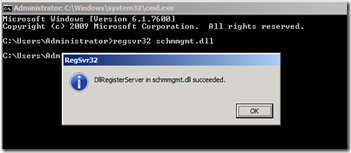
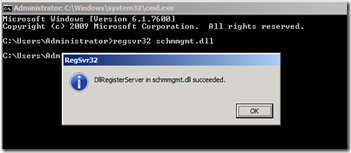
Click Start. Type cmd and press Enter.
Type regsvr32 schmmgmt.dll and press Enter.
Click OK when prompted.
Type Exit and press Enter.
Click Start, type MMC and press Enter.
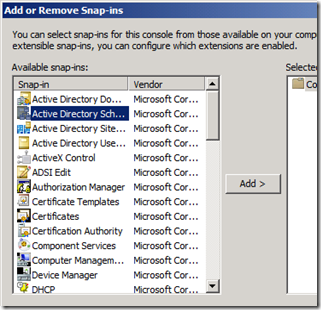
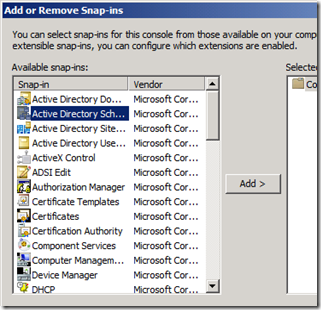
Click File and then click Add\Remove Snap-ins
Click Active Directory Schema and then click Add
Click OK
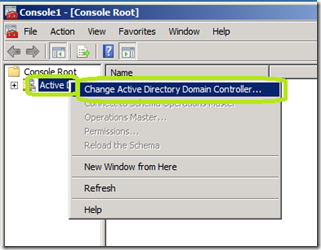
Right click Active Directory Schema and then click Change Active Directory Domain Controller…
Click Type a Directory Server name[:port]here;
Type the DNS name, NetBIOS name, or IP address of the server hosting the AD LDS instance. In this example, the server name is MCT-1.
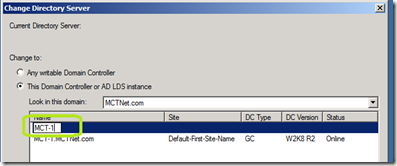
Now click on the enter you just made in the Change Directory Server window and then click OK.
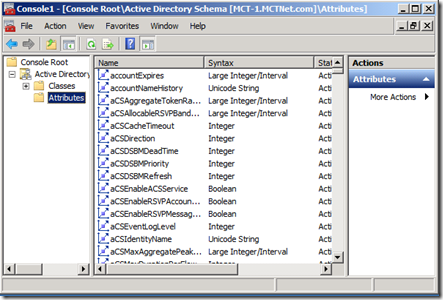
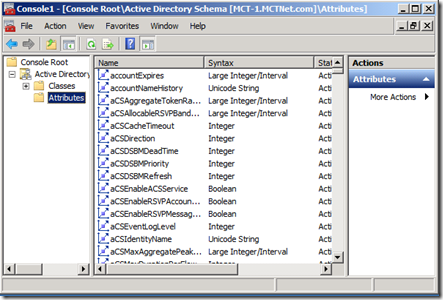
You can now view the classes and attributes of your AD LDS instance.
First you need to register your Schema snap in before we can use it.
Click Start. Type cmd and press Enter.
Type regsvr32 schmmgmt.dll and press Enter.
Click OK when prompted.
Type Exit and press Enter.
Click Start, type MMC and press Enter.
Click File and then click Add\Remove Snap-ins
Click Active Directory Schema and then click Add
Click OK
Right click Active Directory Schema and then click Change Active Directory Domain Controller…
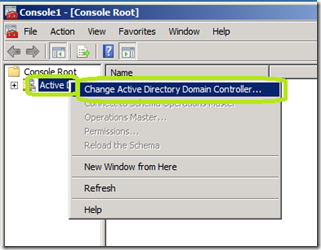
Click Type a Directory Server name[:port]here;
Type the DNS name, NetBIOS name, or IP address of the server hosting the AD LDS instance. In this example, the server name is MCT-1.
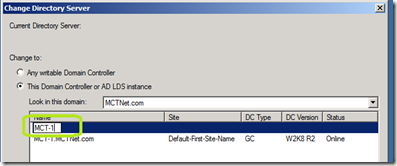
Now click on the enter you just made in the Change Directory Server window and then click OK.
You can now view the classes and attributes of your AD LDS instance.
Comments