PowerShell works in scopes. At the very top layer, you have a global scope. When you run a script, it is ran in a script scope inside the global. If you run any functions inside that script, they run in their own function scope inside the script scope, which is inside the global scope.
When the function is finished and it exits its scope, all the data in the function is lost. When the script ends, all of its data and the knowledge of the existence of the scripts functions are also lost. What if you wanted to keep the functions from the script available to the shell? That is where dot sourcing comes into play.
Let’s take a look at this simple function:
Function Display-Info
{
Write-Host (Get-WmiObject Win32_OperatingSystem).Caption
}
Display-Info
The output of this function, which changes depending on the client it is ran on, is:
Microsoft Windows 7 Ultimate
I know, this is a very simple function. the problem is, after the execution is completed, I cannot use the function again in the shell. To help solve this, I’m going to save this function as Library.ps1. You can name it anything that you want. I’m creating Library.ps1 to hold all the functions that I create and want to use in the shell or to make them available to my other PowerShell scripts.
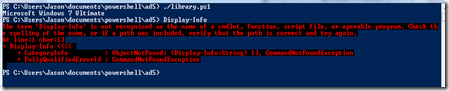
I’m going to run this program in my shell environment.
I’m now going to attempt to execute the function directly from my shell.
No luck.
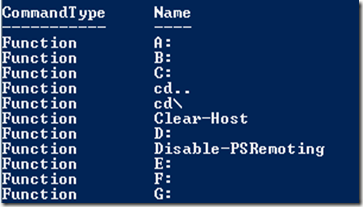
When I execute the command Dir Function: I can see that my function, Display-Info, is not listed.
I’m going to next dot source my library.ps1 script into the shell so that I can use its functions from within the shell and all scripts that I run in that shell session.
To do this, I execute the command . ./library.ps1. Just so we are clear, the command is: Period – Space – Period – forward slash – library.ps1.
Now when I execute Dir Function: I can see my function is listed.
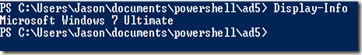
I can now also execute it directly in the shell.
Just remember that once you close the shell, you will need to dot source your PowerShell script back in. The dot sourcing puts the functions in the global scope. When you close the global scope, you lose everything in it.



Comments