Windows 7/2008 R2 have a feature that allows you to join a client to the domain without actually having access to the client. It is called Offline Domain Join. This process involves creating a file on the domain controller and then using that file on the client to join it to the domain. Let’s take a look at how to make that happen.
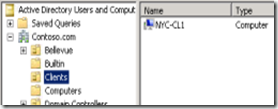
We are going to perform this on the server. The idea is to join a client, NYC-CL1 to the domain in an Organizational Unit called Clients The default container for joining clients to the domain is Computers, but this exercise will allow you to join the client to the OU that you want the computer object to be stored in.
On the Domain Controller, click Start.
Type CMD.
Right click the CMD.exe that appears in the search list and then click Run as Administrator.
Type djoin /provision /domain contoso.com /machine nyc-cl1 /savefile nyc-cl1_File /MachineOU “OU=Clients,DC=contoso,dc=com”
Once this is done, we can see the computer object has been created in the Clients OU.
You now need to copy that file to the machine to be joined.
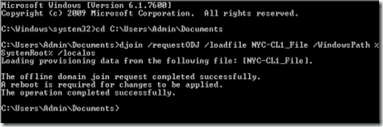
On the client computer, open an elevated command prompt as you did earlier on the server.
Make sure the nyc-cl1_File is accessable in the file structure where you are typing this command line.
Type djoin /requestODJ /loadfile NYC-CL1_File /windowspath %SystemRoot% /localos
You should see a message similar to the one below.
Reboot the client.
Below is Microsoft's information on some of the switches used in this demo.
| /provision | Creates a computer account in AD DS. |
| /domain | Specifies the name of the domain to join. |
| /machine | Specifies the name of the computer that you want to join to the domain |
| /savefile | Saves provisioning data to a file. |
| /machineou | Specifies the name of the organizational unit (OU) in which you want the computer account to be created. By default, the computer account is created in the Computers container. |
| /requestodj | Requests an offline domain join at the next start. |
| /Loadfile | Specifies the output from a previous provisioning command. |
| /windowspath | Specifies the path to the Windows directory of the offline image. If you are using the/localos parameter, specify %systemroot% or %windir% as the value of the/windowspath parameter. |
| /localos | Targets the local operating system installation, instead of an offline image, with the domain join information. If you use this parameter, the value that you specify for/windowspath should be %systemroot% or %windir%. Run this parameter only on a destination computer that you want to join to the domain. This parameter is blocked from being run on a domain controller. Because this parameter injects the blob data into the locally running operating system image, you must restart the computer to complete the domain join operation, as you must also do for an online domain join. |
Comments