When your domain is at least at Windows Server 2008 R1 level, you have the option of using Fine Grain Passwords. In previous implementations of a Windows domain. You were given only only password policy for every users. This was the policy stored in the Default Domain Policy GPO. Now you can have users of different security groups have different password policies that are more fitting to the security of their positions and the data they have access to. One problem that comes up is when a user is a member of multiple security groups, all of which have different PSOs (Password Settings Object – aka Fine grain password policy) assigned to them. The Precedence value assigned to each PSO determines the one in effect. Of all the PSOs the user recieves from their respective PSOs, the User Object only uses the PSO with the lowest precedence value. Here is how to determine which one a user account is using.
On your Domain Controller, open Active Directory Users and Computers.
Click View and make sure there is a check mark beside Advanced Features.
Next browse to the users account object. Right click it and select Properties.
Click the Attribute Editor tab,
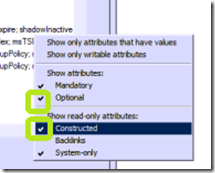
Click the Filter button and make sure there are checks by Show Attributes: Optional and Show read-only attributes: Constructed.
Look for the attribute msDS-ResultantPSO. The name of the PSO being applied to this user is the value of this attribute.


Comments