Cloning allows you to take a virtual machine and make a copy of it. This is a good way to test a new configuration or software installation on a VM without risking taking the VM down. When you create your clone of a VM, it is not generalized. That means it holds the same SID, and all other settings, as the original. For this reason, you will not be able to run this VM in the same network while the original is running. You can transfer the cloned VM to an isolated virtual network for testing. In the isolated network, it will not have contact with the original.
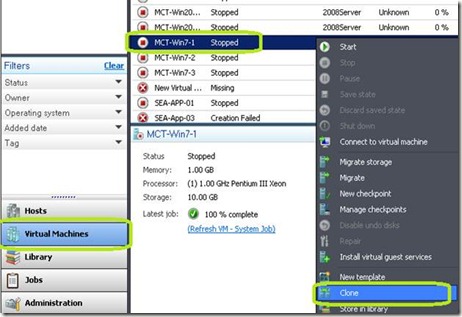
To clone a virtual machine, open Virtual Machine Manager.
Make sure the VM is turned off. The cloning option will not be available if the VM is turned on.
Click Virtual Machines in the lower left hand menu.
Right click the VM that you want to clone and click Clone.
In the Virtual Machine Identity window, you can change the name, description, and owner of this cloned VM.
Click Next
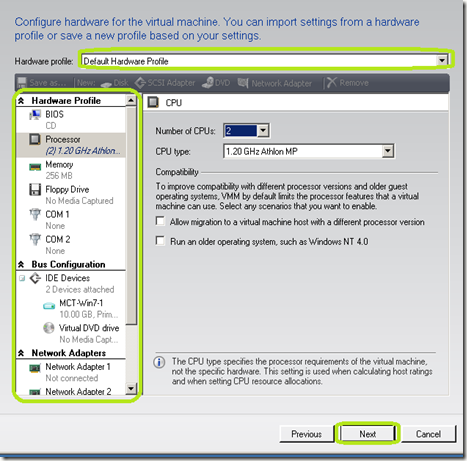
In the Configure Hardware you can keep the hardware profile from the original VM, or make changes such as increasing the RAM, adding processors, or changing BIOS settings. You can also assign the VM a stored hardware profile from the Hardware Profile drop down box.
Click Next
On the Select Destination window, you can place this clone on a host, or place it in a virtual machine library. For this demonstration, I’ve selected Place the virtual machine on a host. Click Next.
In the Select Host window, click the host that you want to store the VM on. Click Next.
On the Select Path window, select the path to store the VM and click Next.
On the Select Networks window, select the virtual networks that each NIC in the VM will connect to. Click Next
On the Summery page, click Create.
The window below will pop up to help you monitor the process.
Depending on the hardware and speed of your network, this process can take some time.


Comments