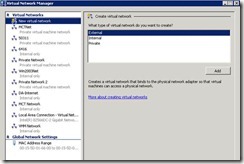
The Virtual Network Manager in Hyper-V allows you to create several types of virtual networks inside your virtual environment. This allows you to create isolated networks inside the same server. Click Virtual Network Manager in the Actions pane to access the Virtual Network Manager.
In the left hand pane is a listing of all the virtual networks currently programed in on this Hyper-V server. Be default, New virtual network is selected. Be clicking on any of the other already configured networks will allow us to make changes to each profile.
Types of virtual networks.
In the Create virtual network area, we see three types of networks that we can create.
External:
An External network creates a virtual network that you bind to a physical network adapter. This allows the VMs in that virtual network to access your physical network. They will be able to talk with each other, get DHCP addresses, and access the internet if those services are provided.
Provide a Name for this virtual network.
It is a good idea to add some notes as to what this virtual network is going to be used for.
From the drop down list, select the physical NIC that this virtual network will bind to. You can only bind a virtual network to 1 NIC. Also, uncheck the Allow management operating system to share this network adapter. In practice, you want to have a separate NIC for the host and each virtual network hosted on that server.
Internal Only
In this configuration, the VMs will be able to talk with each other, and the host operating system. You will have to provide for IP addressing and name resolution services in this scenario.
Private
With this setting the physical host cannot talk to the VMs and vice versa. It completely isolates network communications to only the VMs inside the virtual network.

Comments