The Active Directory Recycle bin was a very welcomed addition to our arsenal of tools. It allowed us to recover objects from the AD Recycle Bin without losing any of their properties. This was don entirely inside of PowerShell. Now on Server 2012, you can perform this functionality in the Active Directory Administrative Center.
You can learn how to enable to AD Recycle Bin here.
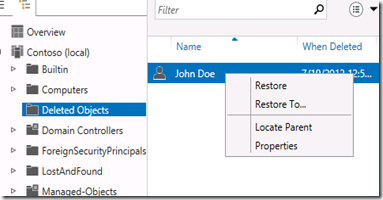
In the image below, you can see a user named John Doe.
We can see that John has the Description property populate with “IT Manager”. Without the AD Recycle Bin, a recovery of this object from a tombstone state would have caused us to lose this data. More importantly, we would have lost the SID associated with this account. Using PowerShell, Lets get the SID of this account for comparison purposes.
We can see the SID ends in 1122. The next step is to delete this object.
Switch the AD Administrative Center to Tree View and then click Deleted Objects.
Right click the object that you want to restore and then click Restore.
The object is restored with all of its properties still intact.




Comments