Windows Server Update Services (WSUS) is a valuable free tool from Microsoft that allows for organizations of any size to manage the updating of their Microsoft products from a central location. One of the challenges that Network Administrators face is a controlled rollout of updates in a manner that allows problems to be addressed without risking the availability of all the clients and servers on the network. WSUS allows for the creation of computer groups. Technically these groups are not Active Directory Groups. In this article, we will see how to target computers in Active Directory groups so they fall into a specified WSUS group.
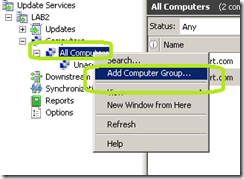
In the image below, you can see the default WSUS groups.
We have a group called All Computers and Unassigned Computers. All Computers is a catch all for all computers. Both those assigned to a group and those that are not are contained in this group. This group allows you to approved updates for all computers in your organization that is managed by WSUS. Unassigned Computers is the catch all for any computer that has not been assigned into a group.
If you want to do staged rollouts of updates, the default configuration will not work. Let’s take a look at how to fix this with Active Directory, Group Policy and WSUS.
First in the WSUS manager, expand Computers.
Right click All Computers and select Add Computer Group.
In the Add Computer Group window, add the name of the WSUS group that you want to have clients placed in via Group Policy. Click Add.
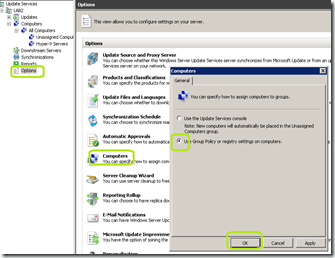
In the WSUS Console, select Options.
Click Computers.
Select Use Group Policy or registry settings on computers.
Click OK
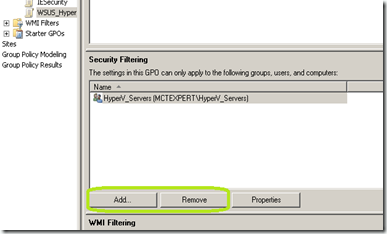
In Active Directory Users and Computers, I have an OU named Groups. Inside this OU I have a group called HyperV_Servers. I have three serves that are a part of this group. Next I’m going to open Group Policy Management Console and create a new GPO called WSUS_HyperV_Servers.
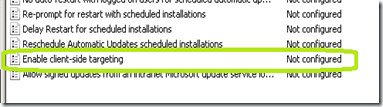
Edit this policy and expand Computer Configureation / Administrative Templates / Windows Components / Windows Update. We are interested in the GPO setting of Enable client-side targeting.
Selected Enabled
Type the name of the WSUS group that you want clients assigned to this policy to be in. This name must match the name of a group that you created in WSUS.
Click OK.
Close the Group Policy Management Editor.
In the Group Policy Management console, make sure your new GPO is selected. Under Security Filtering, remove Authenticated Users and add HyperV_Servers to the group listing.
Now, we need to link this to the Domain. Simply drag and drop the GPO onto the domain (in this case MCTEXPERT.COM) in Group Policy Manager.
Click OK
To speed up the process, run the following commands on the clients.
Gpupdate /force
wuauclt.exe /detectnow
Even after doing this, it may take a few reboots or a couple of hours for everything to start working. The image below has two of the three servers now populating the group.
An alternative method would be to not use security group filtering, but to apply the GPO on an organizational unit that contains the clients that you want to be mapped to a specific WSUS group.




Comments
Thanks for taking the time to compile this