RemoteApp Problem: The Connection was denied because the user account is not authorized for remote login
While attempting to connect to a RemoteApp with a standard user account, you may receive this message:
This can be caused by not having the logged on user as a member of the Remote Desktop Users group on the Remote Desktop Server. Another reason why you may experience this issue is if you are still on the 180 grace period for RDS licensing. To clear up this problem, reboot the RDS server.
if this still does not work while you are in the grace period add the users, or preferably a group, to the allowed list of users who can log into the RDS server.
On the RDS server, Click Start.
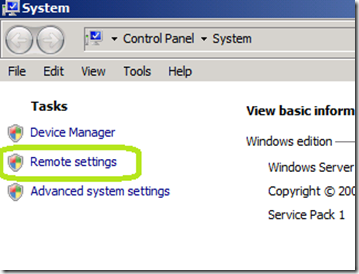
Right click Computer and select Properties
Click Remote Settings
Click Select Users
Click Add.
Add in the User or groups that you want to be able to log in through Remote Desktop Services to this server.
You should be able to access your RemoteApp now.



Comments